Agentic AI Masterclass
Secure AI Agents with Expert-Led Sessions
AI agents aren't waiting for instructions anymore. They're authenticating to your infrastructure, making decisions, and acting on your systems autonomously. The security models we've built over the last twenty years were never designed for that.
Clutch Security’s Agentic AI Masterclass is designed to help CISOs and security teams understand AI agents, their risks, and how to go about securing them.
Module 1
The Ground Shifted
2:05
Episode 1
AI Got Hands
Welcome to the Agentic AI Masterclass. While the industry focused on data leakage and DLP policies, AI started authenticating to infrastructure and acting on its own.

2:55
Episode 2
Contractors Who Don't Ask Questions
AI tools, automation, and agents are three different things. This episode gets precise about the distinction and why it matters for security.

3:30
Episode 3
Four Properties, Zero Precedent
Agents combine four properties no previous technology ever has: autonomy, non-determinism, external manipulability at runtime, and real credentials with real permissions.
2:36
Episode 4
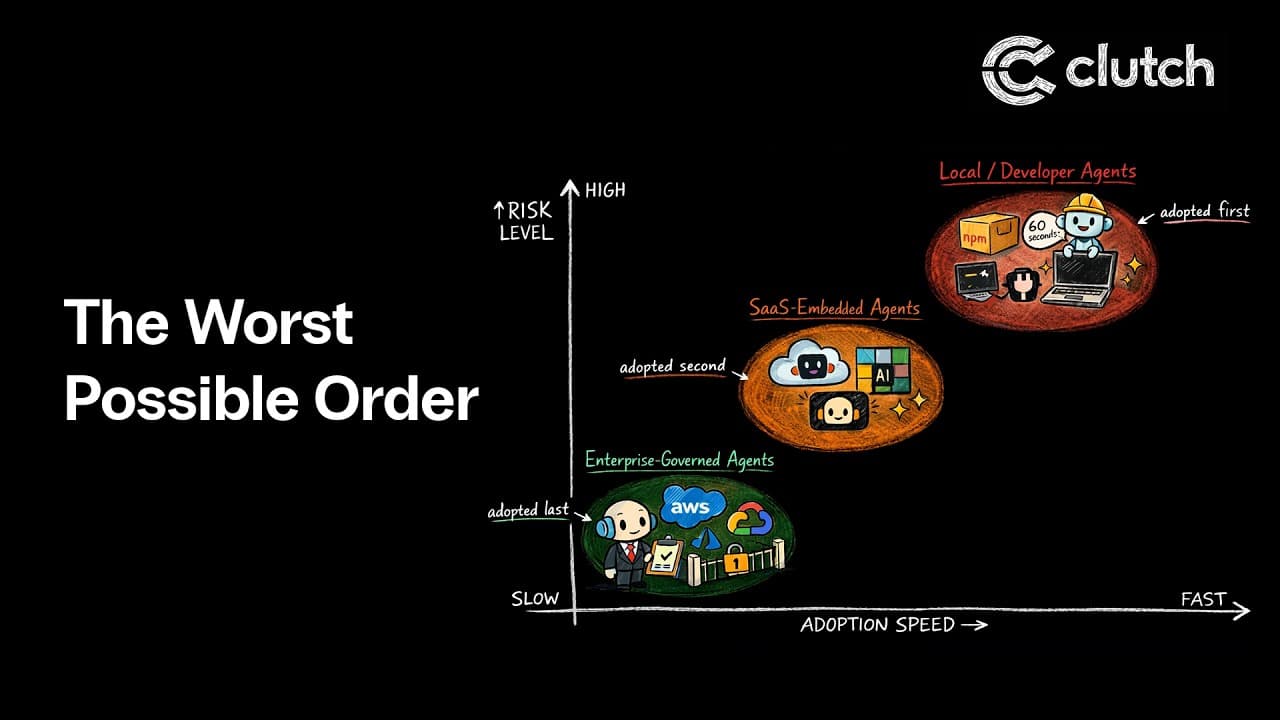
The Worst Possible Order
Agent adoption is happening in the reverse order of safety. The most dangerous category, local developer-driven agents, got adopted first. The safest will get adopted last.
Module 2
Who's Actually Driving
4:22
Episode 5
Neither Human nor Machine
An agent is an autonomous consumer of non-human identities. Securing the agent and securing its credentials are two separate problems that need to be solved together.

3:41
Episode 6
Blind Spots All the Way Down
Every time an agent acts on your infrastructure, five layers are involved: person, agent, tool, identity, resource. No tool in your security stack sees more than one of them.

3:12
Episode 7
The Case of the Curious Crab
In January 2026, open-source agent OpenClaw hit 100,000 GitHub stars in three days. Over 30,000 instances were found exposed publicly, many without basic password protection.
Module 3
Where Things Break
3:42
Episode 8
npm Install Compromise
MCP servers from npm, framework dependencies, poisoned skills, manipulated tool descriptions. The channels through which agents get their capabilities have almost no security verification at any layer.
3:53
Episode 9
Plaintext and Prayers
The most common way agents get credentials is a plaintext config file on a developer's machine. A malicious MCP server doesn't need a zero-day. It just reads the file it was handed.

4:23
Episode 10
Read the Wrong Document, Lose the Kingdom
Prompt injection is OWASP's number one LLM security risk. An attacker embeds instructions in a document or email, and the agent follows them using its legitimate credentials.
Module 4
The Fixes That Aren't
3:45
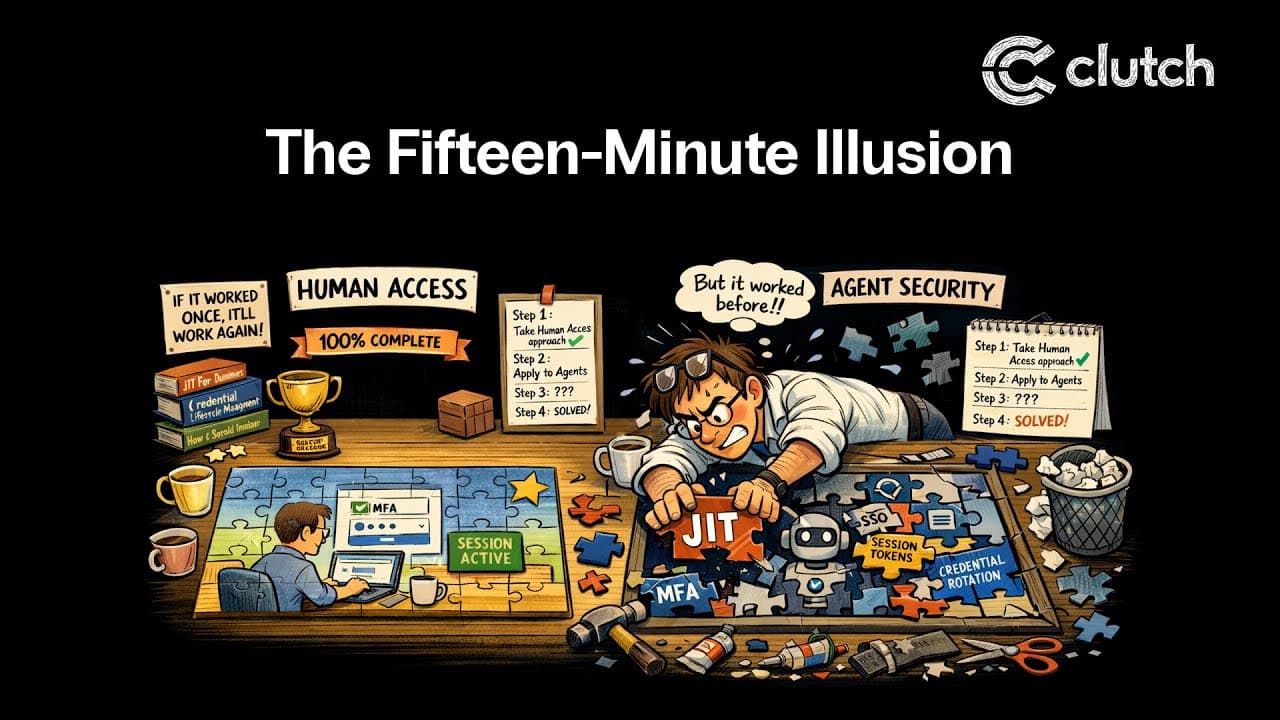
Episode 11
The Fifteen-Minute Illusion
Short-lived credentials are the go-to answer for agent risk. But a prompt-injected agent with a fifteen-minute token can exfiltrate data in seconds.

3:33
Episode 12
Perfectly Scoped, Still Compromised
Strict least privilege sounds like the right answer for agent security. But a prompt-injected agent operating within its authorized permissions is doing everything it's allowed to do.
4:36
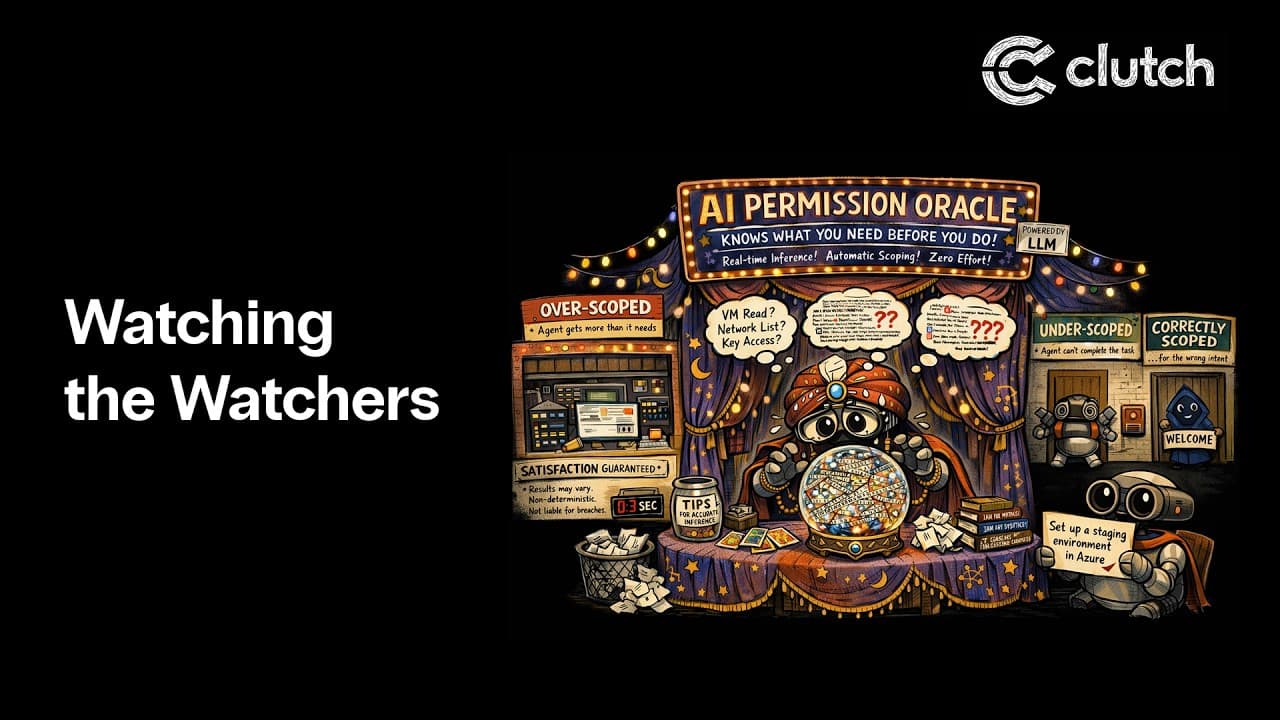
Episode 13
Watching the Watchers
A growing approach proposes using an LLM to monitor agents and generate scoped credentials in real time. The monitoring AI has the same fundamental limitations as the agent it's watching.
Module 5
What Actually Works

2:31
Episode 14
Map the Mess
You need to know what agents are running in your environment before anything else. Discovery and inventory, from Person to Agent to Tool to Identity to Resource, pays off immediately.
3:15
Episode 15
What Normal Looks Like
Discovery is a snapshot. Ongoing governance requires behavioral baselining in destination systems, policies around agent-to-identity mapping, and fast containment when something deviates.
3:32
Episode 16
Honest Answers, Open Questions
A candid close on where the industry actually stands. What you can build today, what's emerging in MCP and prompt injection research, and what remains genuinely unsolved.